$280M Exploit: Drift Protocol Reaches Out to Suspected Attacker Wallets via Blockchain
In response to a $280 million security breach, Drift Protocol has established blockchain-based communication with suspect wallets, while a third-party sender simultaneously applies pressure on the exploiter.

On Friday, Drift Protocol, a decentralized exchange platform operating on Solana's blockchain, announced it had established blockchain-based communication channels with wallet addresses connected to assets taken during the security breach that external security companies have valued at approximately $280 million to $286 million.
Through its official X account, Drift revealed it had begun onchain outreach to wallet addresses currently storing the compromised Ether (ETH), in an effort to establish a communication pathway.
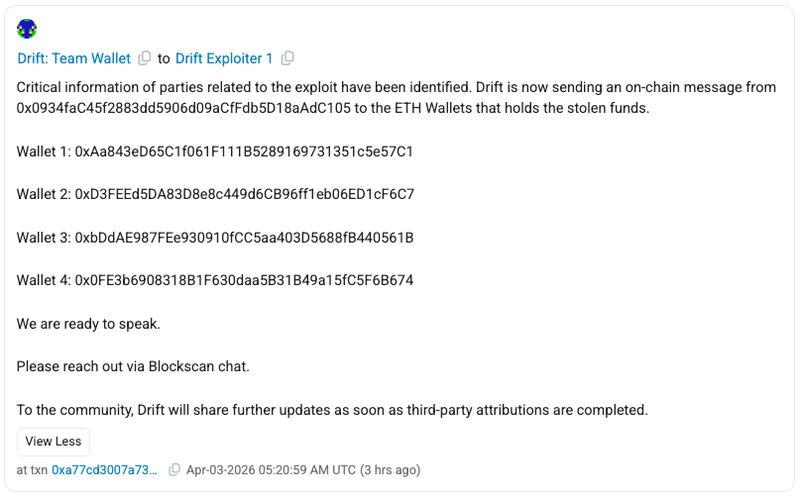
At the time this story was published, the protocol's team had dispatched blockchain messages from their Ethereum wallet address (0x0934faC) to a total of four wallet addresses associated with the person responsible for the exploit, encouraging the perpetrator to make contact through Blockscan chat. "We are ready to speak," the message from Drift stated.
The use of blockchain-based messaging has emerged as a standard approach in responding to security exploits, enabling platforms to establish direct communication channels with perpetrators while maintaining their anonymity. Historical precedents, including the Euler Finance security breach, demonstrate that comparable outreach efforts have resulted in the partial return of compromised assets.
Unidentified party attempts to apply pressure on the perpetrator
The communication effort by Drift followed just hours after an unidentified party operating under the ENS identifier readnow.eth had also made contact with wallet addresses associated with the perpetrator on Thursday through blockchain messaging systems.
This unidentified party asserted they possessed knowledge of the real-world identities of those responsible for the security breach and insisted on receiving 1,000 ETH as payment to keep this information private.
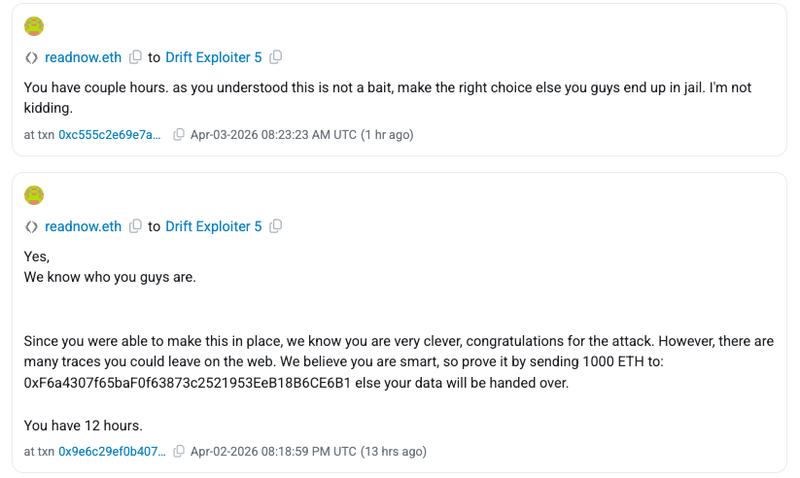
The assertions made in these messages have not been independently confirmed and could potentially be a strategy to deceive or apply pressure to the wallet owner. This development underscores how, in addition to legitimate institutional outreach, unverified communications may proliferate onchain following cryptocurrency security breaches.
Ripple effects across Solana ecosystem continue to expand
Based on data from SolanaFloor, the security breach affecting Drift has impacted no fewer than 20 different protocols built on Solana's blockchain, which includes the decentralized finance (DeFi) service Gauntlet, whose losses were approximated at $6.4 million.
According to Cyvers, a blockchain security monitoring platform, the ramifications continued to grow as of Friday morning, with zero funds being returned 48 hours following the initial attack.
Cyvers characterized the security breach as most likely representing a "weeks-long, staged operation," highlighting that the perpetrator had established durable nonces, a Solana blockchain feature that enables users to cryptographically sign transactions in advance for later execution, several days prior to carrying out the exploit.
"This closely mirrors the Bybit hack, different technique, same root issue: signers unknowingly approving malicious transactions," Cyvers added.
Several industry analysts, including Charles Guillemet, who serves as chief technology officer at Ledger, have proposed the possibility that the security breach may have involvement from threat actors with ties to North Korea, although such details have not been definitively established.