Critical MediaTek Security Flaw Allowed Cryptocurrency Seed Phrase Extraction in Under One Minute
Security researchers from Ledger's Donjon team discovered a critical vulnerability in MediaTek's secure boot mechanism that enabled unauthorized access to sensitive data on specific Android smartphones.

A security vulnerability impacting MediaTek chipsets was addressed by the mobile phone chip manufacturer in January, which previously enabled malicious actors to extract cryptocurrency seed phrases from vulnerable devices with nothing more than a USB cable and specialized software tools.
Ledger's ethical hacking division, Donjon, identified the security weakness and responsibly disclosed the vulnerability to MediaTek prior to the deployment of a security update on Jan. 5. However, Ledger emphasized that users who have yet to apply the most recent security updates should take immediate action to protect their devices.
Test device compromised in 45 seconds
Ledger's analysis revealed that the vulnerability originated within MediaTek's secure boot chain, which is a critical security feature integrated into the company's chipsets designed to guarantee that a mobile device boots up securely and exclusively runs authorized software throughout the initialization process.
In an official statement provided to Cointelegraph, Ledger clarified that the security weakness would allow a threat actor who obtains physical access to an Android smartphone to link it to a computer through a USB connection and circumvent built-in security safeguards, ultimately enabling the extraction of confidential information stored on the device, such as cryptocurrency wallet seed phrases.
Approximately 25% of Android smartphones rely on the Trustonic Trusted Execution Environment (TEE) combined with MediaTek processors, which are the specific components that this security vulnerability targets and exploits.
The Donjon team provided a practical demonstration of the exploit by linking a Nothing CMF Phone 1 device to a laptop computer and successfully breaching the device's security defenses in roughly 45 seconds.
Although Ledger strongly recommended that users install the latest security updates on their devices, a representative from Ledger informed Cointelegraph that they "don't anticipate this to be an ongoing issue."
Mobile phones are never safe, Ledger says
Given that nearly 36 million individuals are storing and managing their digital assets on mobile devices as of early 2025, even a solitary security vulnerability has the potential to compromise a substantial number of cryptocurrency wallets.
In December 2025, Ledger disclosed that its security team had conducted an attack simulation on the MediaTek Dimensity 7300 (MT6878), successfully circumventing its security mechanisms to achieve "full and absolute control over the smartphone, with no security barrier left standing."
Charles Guillemet, Ledger's chief technology officer, shared with Cointelegraph in June 2020 that mobile phones, regardless of whether they run Android or iPhone operating systems, are "very difficult to have secure applications."
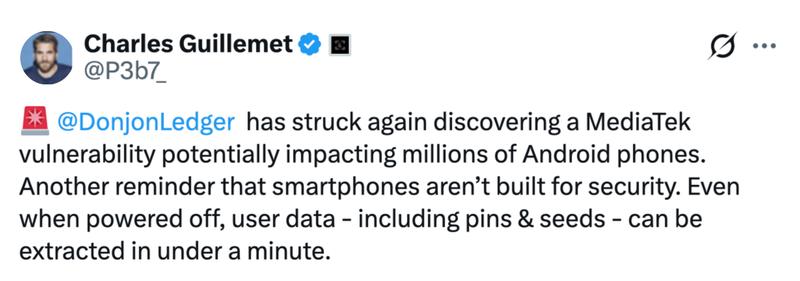
He reiterated a comparable perspective on Wednesday, sharing on X: "Smartphones aren't built for security. Even when powered off, user data - including pins & seeds - can be extracted in under a minute."
This research highlights a fundamental architectural difference: General-purpose chips are built for convenience. Secure Elements are built for key protection. A dedicated Secure Element isolates secrets from the rest of the system, protecting them even under physical attack.