Apple Users Targeted by Sophisticated iPhone Hacking Tool in Cryptocurrency Theft Scheme, Google Reports
Security experts at Google have identified multiple fraudulent cryptocurrency platforms that deploy an advanced exploit framework capable of compromising iPhones to extract digital currency holdings.

Security analysts working within Google's threat detection division have revealed the discovery of a previously unknown exploit framework designed to compromise Apple iPhone devices, with the primary objective of extracting cryptocurrency wallet recovery phrases.
The framework, which its creators have designated "Coruna," is designed to attack iPhones operating on iOS versions ranging from 13.0 through 17.2.1. According to the Google Threat Intelligence Group (GTIG), the kit contains "five full iOS exploit chains and a total of 23 exploits," with several vulnerabilities that had not been previously disclosed to the public, as detailed in their Wednesday report.
According to the research team, their initial encounter with this framework occurred in February 2025, and subsequent monitoring has revealed its deployment by what appears to be a Russian intelligence operation targeting Ukrainian individuals, followed by its appearance on fraudulent Chinese cryptocurrency platforms designed to misappropriate digital assets.
The GTIG emphasized that the framework is incompatible with the most current iOS release and strongly recommended that iPhone owners upgrade their operating systems to the latest available version. For users unable to perform such updates, the organization suggests enabling "Lockdown Mode," a security feature that Apple describes as capable of defending against advanced cyberattacks.
Kit targets crypto via fake websites
According to GTIG, their initial discovery of portions of an iOS vulnerability exploitation occurred in February 2025, during which they observed a surveillance company client utilizing JavaScript to identify device characteristics and deploy the corresponding exploit.
Subsequently during the same year, investigators identified the identical JavaScript infrastructure concealed within several compromised Ukrainian web properties, which was "only delivered to selected iPhone users from a specific geolocation."
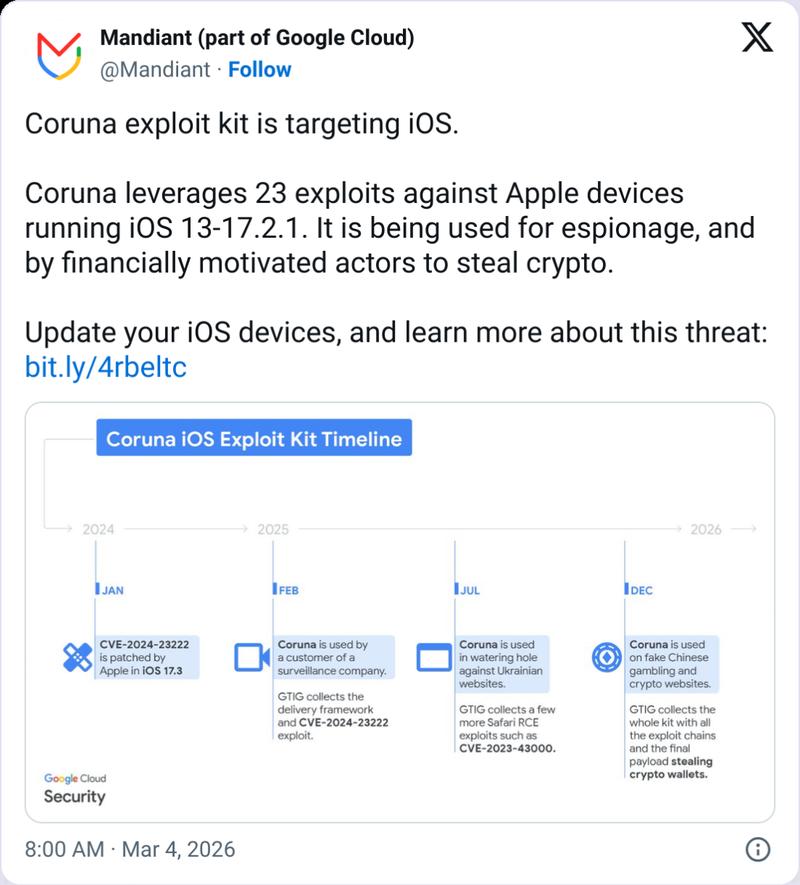
The GTIG team subsequently identified the identical infrastructure in December "on a very large set of fake Chinese websites mostly related to finance," among them a site impersonating the cryptocurrency trading platform WEEX.
Upon accessing these deceptive websites using an iOS-powered device, the infrastructure deploys the exploitation framework and conducts searches for financial data, including scanning text messages for recovery phrases and search terms such as "backup phrase" or "bank account."
Additionally, the framework actively searches for widely-used cryptocurrency applications, including Uniswap and MetaMask, with the intent to steal digital currency holdings or confidential user data.
Coruna's US intelligence origins debated
While GTIG refrained from identifying the specific client of the surveillance firm from which the exploitation framework allegedly emerged, mobile security firm iVerify indicated to WIRED that it may have been developed or acquired by United States government agencies.
"It's highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government,"
iVerify co-founder Rocky Cole told WIRED
"This is the first example we've seen of very likely US government tools — based on what the code is telling us — spinning out of control and being used by both our adversaries and cybercriminal groups."
However, Kaspersky's principal security researcher told The Register that the cybersecurity company saw "no evidence of actual code reuse in the published reports to support attributing Coruna to the same authors."
