Cybercriminals Deploy 'ClickFix' Strategy, Masquerading as Venture Capitalists in Sophisticated Cryptocurrency Heists
While the ClickFix method became widely adopted by cryptocurrency cybercriminals in recent times, cybersecurity experts have monitored its evolution since 2024, with victims found across multiple sectors.

Cybercriminals targeting cryptocurrency holders with so-called "ClickFix" attack methods have evolved their tactics to include posing as representatives from venture capital companies and compromising browser extensions in their latest two offensive campaigns.
A cybersecurity intelligence report released Monday by Moonlock Lab reveals that bad actors are leveraging fabricated venture capital entities including SolidBit, MegaBit and Lumax Capital. These fraudsters utilize these fake firms to initiate contact with potential victims through LinkedIn, presenting partnership opportunities before directing them toward counterfeit Zoom and Google Meet conference links.
Upon clicking the malicious hyperlink, victims find themselves redirected to what appears to be a legitimate event page that displays a fabricated Cloudflare "I'm not a robot" verification box. When users click this deceptive checkbox, a harmful command is automatically transferred to their clipboard, and they receive instructions to launch their computer's command terminal and input the purported verification code, thereby triggering the malicious attack sequence.
"The ClickFix technique is what makes the final step so effective," the Moonlock Lab team said. "By turning the victim into the execution mechanism—having them paste and run the command themselves—the attackers sidestep the very controls the security industry has spent years building. No exploit. No suspicious download."
According to Moonlock Lab's investigation, an individual operating under the identity Mykhailo Hureiev, who is presented as the co-founder and managing partner at SolidBit Capital, has served as a key contact person during the LinkedIn outreach portion of this fraudulent scheme. Additionally, two X users have come forward reporting questionable interactions with an account bearing the Hureiev name.

Nevertheless, Moonlock Lab emphasizes that the operation's underlying infrastructure demonstrates advanced sophistication and appears engineered to cycle through different identities whenever one fraudulent persona becomes publicly exposed.
Chrome extension hijacked to steal crypto
In a separate but related development, cryptocurrency thieves have recently distributed a compromised Chrome extension utilizing a "ClickFix" attack methodology.
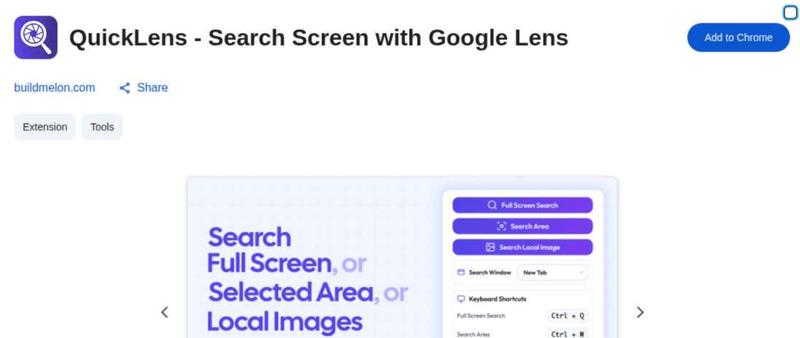
The QuickLens extension, which provides users with functionality to conduct Google Lens searches directly within their browser environment, was pulled from the web store following its compromise that enabled malware distribution, as detailed in a Feb. 23 report by John Tuckner, who founded the cybersecurity firm Annex Security.
Following a change in QuickLens ownership that occurred on Feb. 1, a newly updated version was published approximately two weeks afterward that incorporated malicious code designed to execute ClickFix attacks alongside additional information-harvesting tools. According to Tuckner's findings, the extension had accumulated approximately 7,000 active users at the time of compromise.
The compromised extension was programmed to actively hunt for cryptocurrency wallet information and seed phrases with the objective of stealing digital assets. Beyond cryptocurrency theft, it also extracted complete Gmail inbox contents, harvested YouTube channel information, and captured various login credentials and payment details that users entered into online forms, as documented in an eSecurity Planet report published on March 2.
ClickFix attacks are used to target many industries
According to Moonlock Lab's analysis, the ClickFix methodology has experienced growing adoption among malicious actors since the previous year, primarily because it compels victims to manually execute the harmful payload themselves, thereby circumventing conventional security tools and defenses.
That said, cybersecurity researchers have been monitoring and documenting its deployment since at least 2024, with targeted victims distributed across a diverse spectrum of industries and sectors.
In August of the previous year, Microsoft Threat Intelligence issued a public advisory warning that its teams had been monitoring "campaigns targeting thousands of enterprise and end-user devices globally every day."
At the same time, Unit42, a cyber threat intelligence organization, documented in a July report from last year that this "relatively new social engineering technique" had been affecting various sectors including manufacturing, wholesale and retail, state and local governments, and utilities and energy.