Understanding BIP-360: Bitcoin's Strategy for Quantum Threat Mitigation
BIP-360 brings P2MR technology to Bitcoin, addressing quantum computing vulnerabilities. Explore the modifications it implements, its limitations, and the compromises involved.

Core highlights
- For the first time, BIP-360 formally integrates quantum resistance into Bitcoin's development trajectory. The proposal signifies a careful, gradual advancement rather than a sweeping transformation of the underlying cryptographic framework.
- The primary quantum vulnerability targets public keys that have been disclosed, not the SHA-256 hash function used in Bitcoin, establishing public key disclosure as the main weak point that developers seek to minimize.
- Pay-to-Merkle-Root (P2MR) is the innovation brought by BIP-360, eliminating Taproot's key path spending mechanism and requiring all transactions to utilize script paths, thereby reducing elliptic curve cryptography exposure.
- The capability to execute smart contracts remains fully operational, as P2MR continues to accommodate multisignature arrangements, time-based restrictions, and sophisticated custody configurations through Tapscript Merkle tree structures.
Bitcoin's architecture was designed to survive adversarial conditions spanning economic, political, and technological domains. As of March 10, 2026, the development community is taking steps to address an evolving challenge: the rise of quantum computing capabilities.
With the recent release of Bitcoin Improvement Proposal 360 (BIP-360), quantum resistance has been formally incorporated into Bitcoin's technical development agenda for the first time. Although certain media coverage characterizes this as a revolutionary transformation, the actual approach is considerably more cautious and progressive.
This analysis examines how BIP-360 implements Pay-to-Merkle-Root (P2MR) to diminish Bitcoin's vulnerability to quantum threats by eliminating Taproot key path transactions. The discussion covers the enhancements the proposal delivers, the compromises it necessitates, and the reasons it falls short of rendering Bitcoin entirely post-quantum secure.
The quantum computing threat to Bitcoin explained
Bitcoin's security framework relies on cryptographic methods, chiefly the Elliptic Curve Digital Signature Algorithm (ECDSA) alongside Schnorr signatures that arrived with Taproot. Classical computing systems cannot feasibly calculate a private key when given only its corresponding public key. A sufficiently advanced quantum computer executing Shor's algorithm, however, could compromise elliptic curve discrete logarithms, thereby revealing those private keys.
Important distinctions to understand:
- Public-key cryptography faces the most severe quantum threats, whereas hashing algorithms are more resilient.
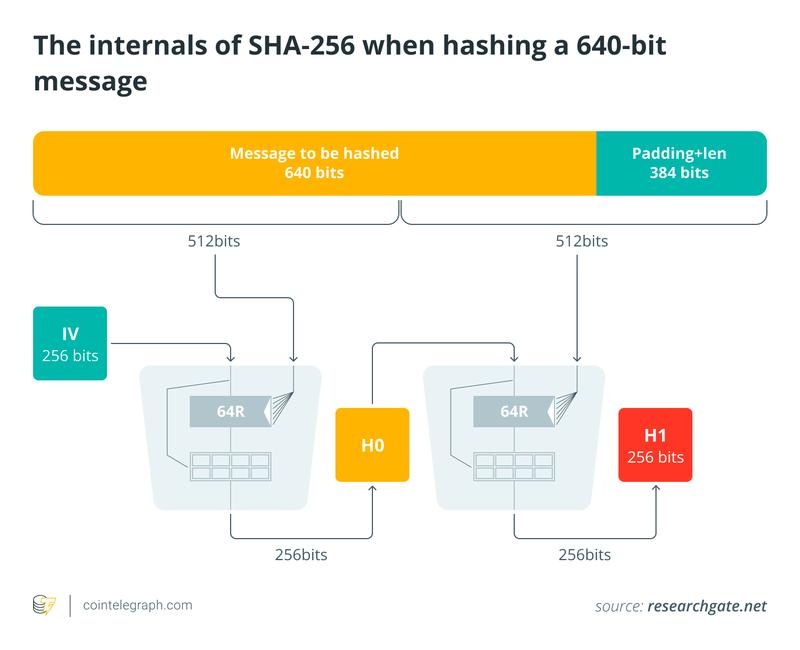
- SHA-256, which Bitcoin employs, maintains considerable strength against quantum approaches. Grover's algorithm only achieves a quadratic acceleration rather than exponential gains.
- The genuine vulnerability emerges when public keys are disclosed on the blockchain ledger.
Consequently, the developer community concentrates on public key disclosure as the predominant quantum vulnerability pathway.
Current Bitcoin weaknesses in 2026
Different address formats within the Bitcoin ecosystem present varying degrees of susceptibility to potential quantum attacks:
- Addresses used multiple times: When coins are spent, the public key becomes visible on the blockchain, creating exposure to a future cryptographically relevant quantum computer (CRQC).
- Original pay to public key (P2PK) outputs: Bitcoin's earliest transactions included public keys directly within transaction outputs.
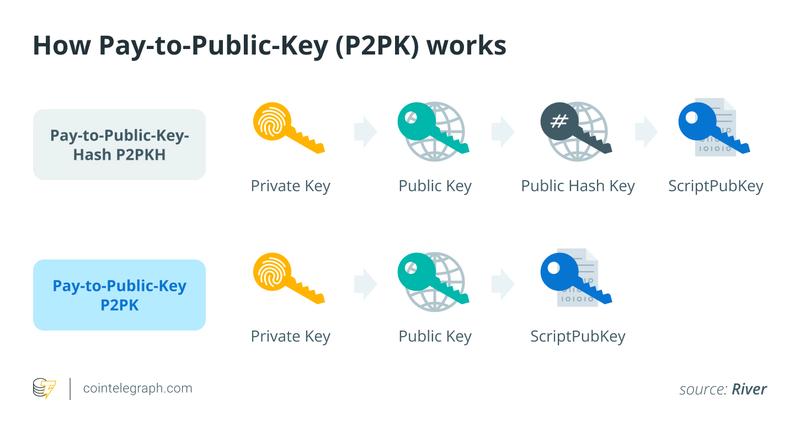
- Taproot key path transactions: Taproot (activated in 2021) provides two spending mechanisms: an efficient key path (which reveals a modified public key upon spending) or a script path (which discloses scripts through a Merkle proof). The key path represents the primary theoretical vulnerability under quantum attack scenarios.
BIP-360's focus is specifically on mitigating that key path vulnerability.
P2MR: BIP-360's core innovation
BIP-360 establishes a new output format called Pay-to-Merkle-Root (P2MR), which closely resembles Taproot but incorporates one crucial modification. The key path spending mechanism is completely eliminated.
Rather than creating a commitment to an internal public key as Taproot does, P2MR creates a commitment exclusively to the Merkle root derived from a script tree. Spending requires:
- Disclosure of a script leaf
- Submission of a Merkle proof demonstrating its membership in the committed root
No spending pathway based on public key signatures exists whatsoever.
Removing key path transactions achieves:
- Zero public key exposure for simple signature verification.
- Complete reliance on hash-based commitments for all spending paths.
- Substantial reduction in long-term elliptic curve public key vulnerability.
Hash-based cryptographic methods demonstrate significantly greater resistance to quantum attacks compared to elliptic curve cryptography. This dramatically reduces the potential attack surface.
Capabilities preserved under BIP-360
A frequent misunderstanding suggests that eliminating key path spending diminishes smart contract functionality or scripting capabilities. This is incorrect. P2MR maintains complete support for:
- Multisignature configurations
- Time-locked transactions
- Payments with conditions
- Estate planning arrangements
- Sophisticated custody solutions
BIP-360 implements all these capabilities through Tapscript Merkle tree structures. While full scripting functionality is preserved, the streamlined yet vulnerable direct signature mechanism is removed.
Did you know? Satoshi Nakamoto briefly acknowledged quantum computing in early forum discussions, suggesting that if it became practical, Bitcoin could migrate to stronger signature schemes. This shows that upgrade flexibility was always part of the design philosophy.
Real-world effects of implementing BIP-360
While BIP-360 might appear to be a strictly technical adjustment, its consequences would extend to wallet providers, cryptocurrency exchanges, and custody service levels. Upon activation, it would progressively transform how new Bitcoin outputs are generated, transacted, and protected, particularly for users who prioritize long-term quantum resilience.
- Wallet applications could offer voluntary P2MR address formats (presumably beginning with "bc1z") as a "quantum-resistant" option for newly received coins or extended holding periods.
- Transaction sizes will increase modestly (additional witness data from script path requirements), which could elevate transaction fees compared to Taproot key path transactions. This represents a security-efficiency tradeoff.
- Complete deployment would necessitate modifications across wallets, exchanges, custodial services, and hardware wallet devices. Preparation timelines should extend multiple years ahead.
Did you know? Governments are already preparing for "harvest now, decrypt later" risks, where encrypted data is stored today in anticipation of future quantum decryption. This strategy mirrors concerns about exposed Bitcoin public keys.
BIP-360's explicit limitations
Although BIP-360 fortifies Bitcoin against future quantum capabilities, it does not constitute a comprehensive cryptographic redesign. Recognizing its boundaries is equally critical to understanding its contributions:
- Existing coins require manual migration: Previously created unspent transaction outputs (UTXO) retain their vulnerability until owners actively transfer funds to P2MR outputs. Successful migration relies entirely on user initiative.
- Current signature algorithms remain unchanged: BIP-360 does not substitute ECDSA or Schnorr with lattice-based algorithms (such as Dilithium or ML-DSA) or hash-based alternatives (such as SPHINCS+). It exclusively addresses the Taproot key path vulnerability pattern. Transitioning Bitcoin's base layer to post-quantum signature schemes would demand substantially more extensive modifications.
- Complete quantum protection is not achieved: An unexpected CRQC breakthrough would still necessitate extensive coordination involving miners, node operators, exchanges, and custodians. Inactive coins could generate complicated governance challenges, and network congestion could result.
The rationale for immediate action
Quantum computing advancement timelines remain uncertain. Some experts project decades before practical threats emerge. Others reference IBM's fault-tolerant quantum computing objectives for the late 2020s, Google's recent chip innovations, Microsoft's topological qubit research, and US government migration schedules targeting 2030-2035.
Infrastructure transitions of this magnitude require extended timeframes. Bitcoin's development community emphasizes comprehensive planning spanning BIP specification, software implementation, infrastructure deployment, and user adoption phases. Delaying action until quantum threats become definitive could leave inadequate time for necessary infrastructure transformations.
Should community consensus emerge, a staged soft fork deployment might proceed as follows:
- Activation of the P2MR output format
- Integration of support across wallets, exchanges, and custodial platforms
- Progressive user migration spanning multiple years
This pattern resembles the voluntary adoption followed by widespread acceptance observed with SegWit and Taproot deployments.
Ongoing discussions surrounding BIP-360
Discussion persists regarding implementation urgency and associated costs. Key questions under consideration include:
- Will long-term holders accept marginally higher transaction fees?
- Should institutional participants spearhead the migration effort?
- How should unmoved coins be addressed?
- What approaches should wallets employ to communicate "quantum protection" without generating unwarranted concern?
This represents an active, evolving dialogue. BIP-360 moves the conversation forward but does not resolve all questions.
Did you know? The idea that quantum computers could threaten cryptography dates back to 1994, when mathematician Peter Shor introduced Shor's algorithm, long before Bitcoin existed. Bitcoin's future quantum planning is essentially a response to a 30-year-old theoretical breakthrough.
Recommended actions for users today
Quantum threats remain distant, so immediate alarm is unwarranted. Sensible precautions you might implement include:
- Never reuse addresses
- Stick to up-to-date wallet software
- Follow protocol upgrade news
- Watch for P2MR support in wallets
Individuals managing substantial holdings should methodically assess their exposure profiles and develop contingency strategies.
BIP-360: Initiating Bitcoin's quantum defense
BIP-360 marks Bitcoin's inaugural formal measure toward diminishing quantum vulnerability at the protocol foundation. It restructures how new outputs may be constructed, reduces public key disclosure incidents, and establishes the framework for extended migration planning.
The proposal does not automatically modify existing coins, preserves currently deployed signature mechanisms, and highlights the requirement for methodical, coordinated ecosystem-wide implementation. Achieving genuine quantum resistance will result from continuous engineering efforts and gradual adoption phases, not from any single BIP.
