2029 Deadline Set by Google for Post-Quantum Cryptography Shift Amid Growing Security Concerns
As Google advances development of Willow, among today's leading superconducting quantum processors, the tech giant calls on industry peers to expedite their post-quantum cryptography transitions.

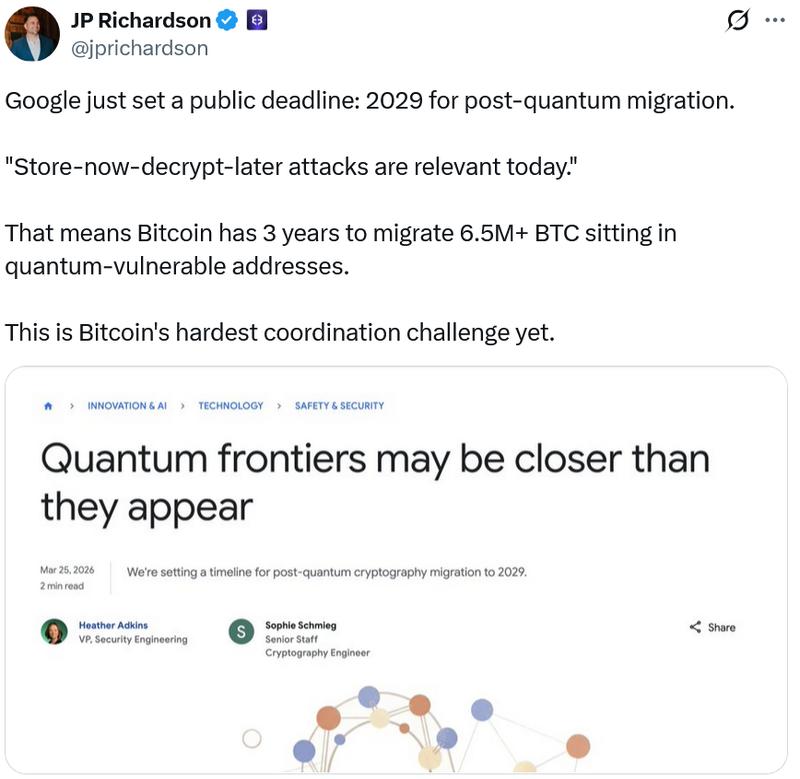
A firm 2029 target has been established by Google for completing its transition to post-quantum cryptography (PQC), with the company cautioning that the "quantum frontiers" may arrive sooner than anticipated.
In a Wednesday announcement, Google explained that swift advancements in quantum computing technology and quantum error correction capabilities, combined with revised projections regarding the speed at which quantum machines could compromise existing encryption protocols, have amplified the need for immediate action.
"Quantum computers will pose a significant threat to current cryptographic standards, and specifically to encryption and digital signatures," Google said, while also noting that PQC migration is needed for users to use authentication services securely.
Marking the first occasion Google has publicly committed to a specific timeframe for implementing post-quantum protections throughout its product lineup, the 2029 target precedes many industry predictions for Q-Day — the moment when quantum computing systems achieve sufficient power to crack existing public-key encryption methods.
"It's our responsibility to lead by example and share an ambitious timeline. By doing this, we hope to provide the clarity and urgency needed to accelerate digital transitions not only for Google, but also across the industry."
The urgency emphasized by Google arrives as the company pushes forward with developing Willow, its quantum chip that boasts a computational power of 105 qubits, positioning it among the industry's most formidable processors.
Simultaneously, mounting anxieties suggest that quantum computing systems could cause substantial disruption throughout the cryptocurrency sector by compromising the cryptographic algorithms that safeguard digital assets. Nevertheless, ongoing discussions continue regarding whether the vulnerability is limited exclusively to crypto wallets with revealed public keys or if all coins face potential exposure.
Crypto networks also eye post-quantum upgrades
On Tuesday, the Ethereum Foundation unveiled a "Post-Quantum Ethereum" resource hub, dedicated to safeguarding the blockchain against emerging quantum computing risks and preserving the billions of dollars in value maintained on the network.
By 2029, the post-quantum team intends to integrate quantum-resistant technologies into Ethereum at the protocol level, with additional solutions aimed at the execution layer to be implemented subsequently.
During January 2025, Solana developers constructed a quantum-resistant vault on the Solana blockchain designed to safeguard user assets from quantum vulnerabilities by deploying an advanced hash-based signature system that creates fresh keys for every transaction executed.
Nevertheless, accessing this feature requires Solana users to maintain their funds within Winternitz vaults instead of standard Solana wallets, given that the solution does not constitute a network-wide security enhancement.
At the same time, growing disagreement has emerged within the Bitcoin ecosystem regarding the appropriate measures developers should pursue, if any action is warranted at all.
Adam Back, Blockstream CEO and one of the Bitcoin ecosystem's most influential figures, maintains that quantum risks are substantially exaggerated and that no intervention will be necessary for several decades.
Conversely, security researcher Ethan Heilman alongside other experts have put forward a novel output type for Bitcoin, designated Pay-to-Merkle-Root, via Bitcoin Improvement Proposal 360 (BIP-360), designed to shield Bitcoin addresses from possible short-exposure quantum attacks.
That said, implementing this solution could require as long as seven years, according to Heilman's statement to Cointelegraph in February.