Swedish Authorities Launch Investigation Into Alleged E-Government Platform Code Breach
Following claims by cybercriminals that they successfully obtained and published source code from Sweden's digital government infrastructure, authorities have initiated an investigation involving CGI Sverige.

Swedish officials have launched an investigation after a cybercriminal group alleged they successfully obtained and released source code along with additional confidential materials connected to the nation's digital government infrastructure, leading to a coordinated incident response from CGI Sverige and government agencies.
Reports emerged on Thursday from cybersecurity sources on X and Swedish media outlets indicating that a hacking group identifying itself as ByteToBreach had released materials allegedly obtained from CGI Sverige, which operates as the Swedish arm of the international information technology corporation CGI Group, along with data from Sweden's electronic government systems, as documented by Swedish news source Aftonbladet.
In a statement to Aftonbladet, CGI revealed that their information security division identified a security breach affecting a pair of internal testing servers located in Sweden that were not deployed in live production environments. According to the company's disclosure, an outdated version of an application along with its corresponding source code had been left accessible, though the firm stated they found no evidence suggesting that client production information or active operational systems had been compromised. Agneta Hansson, serving as press secretary for CGI, verified to the publication that government authorities have opened an investigation into the data exposure incident.
Digital government services in Sweden were utilized by approximately 95% of the nation's 10.7 million residents during 2024, based on statistics compiled by Eurostat.
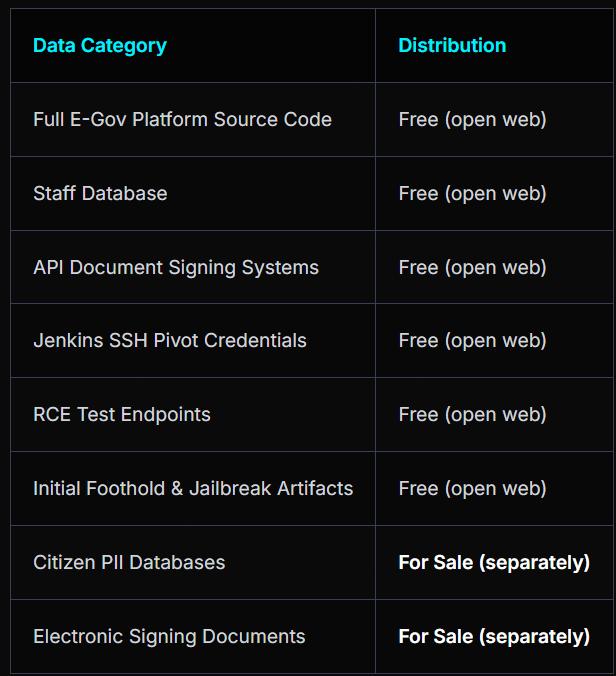
The compromised materials potentially encompass the platform's underlying source code along with configuration documents, internal employee information databases, databases containing personally identifiable information belonging to Swedish citizens, digital signature documentation, and additional classified information.

Cointelegraph reached out to both CGI Group and Sweden's national information technology incident response center, CERT-SE, seeking official statements regarding the reported data breach.
Swedish civil defense minister confirms cybersecurity incident
Meanwhile, Carl-Oskar Bohlin, who serves as Sweden's minister responsible for civil defense matters, acknowledged the occurrence of the data breach and indicated that governmental bodies are collaborating with CERT-SE alongside the National Cyber Security Center in efforts to determine the identities of those responsible for the attack.
Anders Nilsson, an expert specializing in information technology security, verified that the compromised materials appeared to be legitimate. "Source code for several programs seems to exist, and from what I can see, the hack looks genuine," Nilsson wrote in an email to media outlet SVT.
Hackers target Swedish and European infrastructure
Cybercriminal groups are progressively focusing their attacks on publicly accessible digital infrastructure across Sweden and throughout the broader European region, according to warnings issued by Threat Landscape, a threat intelligence monitoring platform.
"This is not an isolated incident," the platform said in a Thursday report.
ByteToBreach is the same actor responsible for the Viking Line breach posted just one day prior, suggesting an ongoing campaign targeting Swedish and European infrastructure via CGI's managed services footprint.
The cybercriminal organization made assertions that they had successfully released the complete source code belonging to the electronic government platform, while providing numerous supporting documents and materials as evidence of their claims.
Security researchers specializing in threat intelligence indicated that the data exposure incident could potentially result in downstream security risks should malicious actors leverage the compromised code or technical documentation to discover vulnerabilities within systems that face public networks, although the complete contents of the released data package have not yet undergone independent verification processes.
